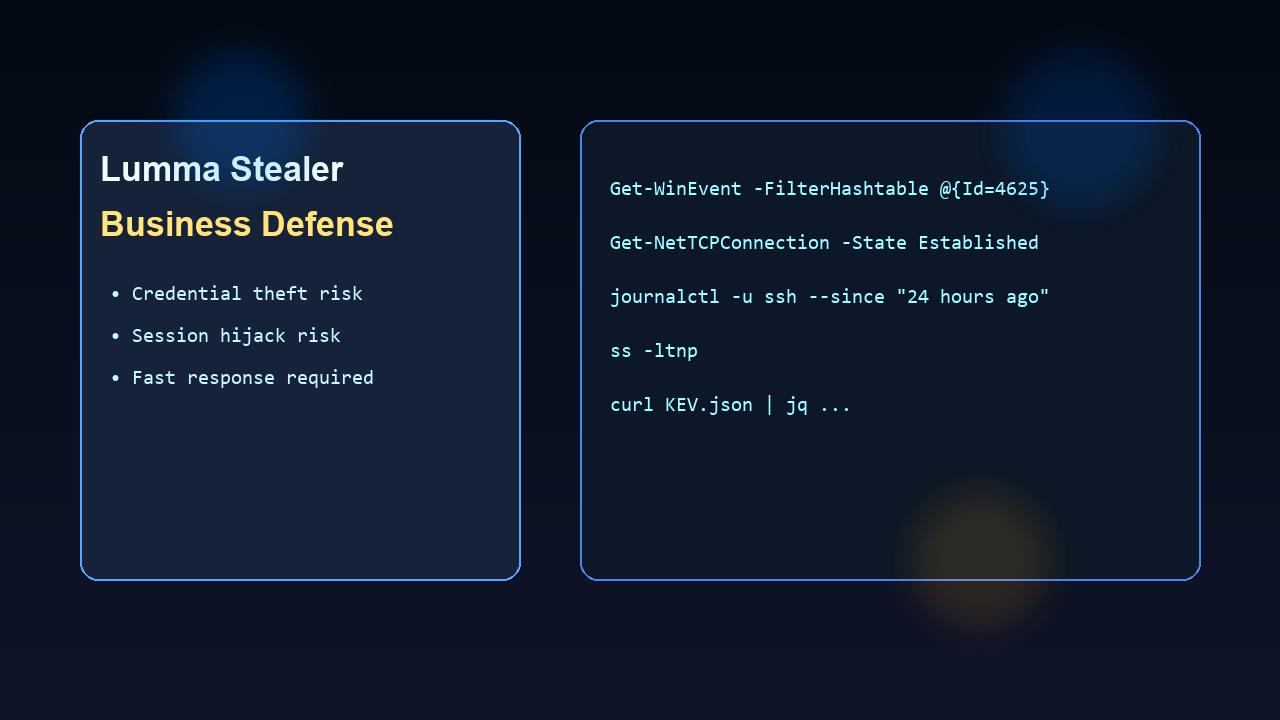
Lumma Stealer is an information-stealing malware family focused on browser credentials, session cookies, wallet data, and endpoint fingerprints. In business environments, that often leads to account takeover in Microsoft 365, VPN, admin portals, and finance tooling.
This guide gives a practical prevention + response checklist with commands you can run now.
What Lumma typically steals
- Saved browser credentials
- Session cookies/tokens
- Autofill data
- Wallet extension data
- Host/network inventory details
High-value prevention controls
- Enforce MFA and Conditional Access on all business-critical apps
- Disable browser-saved passwords for business accounts
- Restrict local admin rights on endpoints
- Use EDR with behavioral detection enabled
- Block risky file types and suspicious download sources
Useful commands for rapid triage
Windows: suspicious logons and services
# Failed logons (last 24h)
Get-WinEvent -FilterHashtable @{LogName='Security'; Id=4625; StartTime=(Get-Date).AddHours(-24)} |
Select-Object TimeCreated, Id, Message -First 50
# Successful logons (last 24h)
Get-WinEvent -FilterHashtable @{LogName='Security'; Id=4624; StartTime=(Get-Date).AddHours(-24)} |
Select-Object TimeCreated, Id, Message -First 50
# Newly installed services (last 24h)
Get-WinEvent -FilterHashtable @{LogName='System'; Id=7045; StartTime=(Get-Date).AddHours(-24)} |
Select-Object TimeCreated, Message -First 50Windows: process/network correlation
# Established outbound connections + owning PID
Get-NetTCPConnection -State Established |
Select-Object LocalAddress,LocalPort,RemoteAddress,RemotePort,OwningProcess
# Map process details
Get-CimInstance Win32_Process |
Select-Object ProcessId, ParentProcessId, Name, CommandLineLinux: auth and process checks
# SSH/auth activity
sudo journalctl -u ssh --since "24 hours ago"
# Failed/successful auth lines (Debian/Ubuntu)
sudo grep -E "Failed password|Accepted" /var/log/auth.log | tail -n 200
# Listening services
sudo ss -ltnp
# Active network connections
sudo ss -tpnKEV prioritization (CISA feed)
curl -s https://www.cisa.gov/sites/default/files/feeds/known_exploited_vulnerabilities.json | jq '.vulnerabilities[] | {cveID, vendorProject, product, dateAdded}' | head -n 40If infection is suspected: immediate response
- Isolate the endpoint from network.
- Revoke active sessions/tokens for affected users.
- Reset passwords and re-check MFA posture.
- Hunt for mailbox, VPN, and admin portal abuse.
- Rebuild compromised endpoint from clean baseline.
30-minute business checklist
- MFA coverage verified for critical apps
- EDR healthy and reporting on all endpoints
- Recent failed logons reviewed
- Unknown services/processes reviewed
- Token/session revocation procedure tested
Bottom line: Lumma is an identity compromise catalyst. The fastest risk reduction comes from layered endpoint controls + identity hardening + quick token/credential response playbooks.
References
- CISA Known Exploited Vulnerabilities (KEV) Catalog
- CISA StopRansomware Guidance
- MITRE ATT&CK Knowledge Base